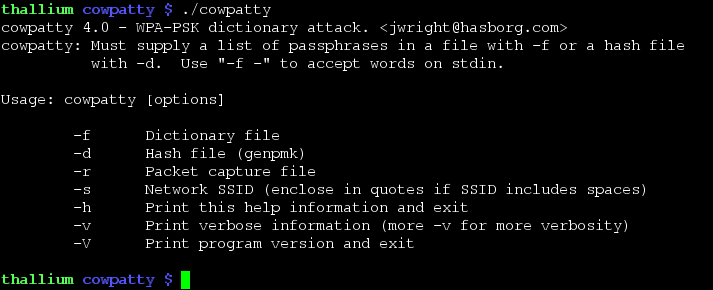
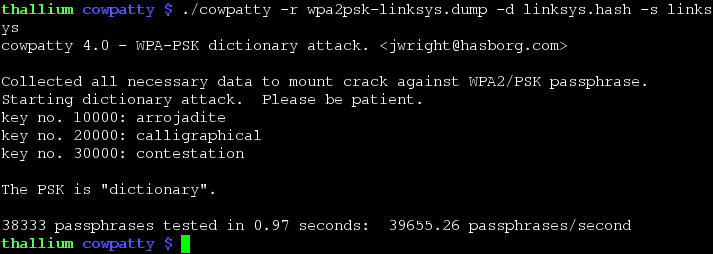
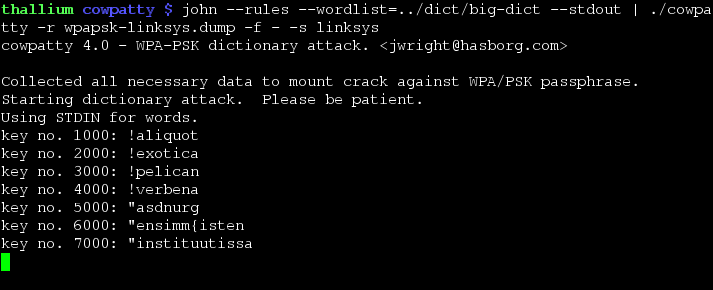
Implementation of an offline dictionary attack against WPA/WPA2 networks using PSK-based authentication (e.g. WPA-Personal). Many enterprise networks deploy PSK-based authentication mechanisms for WPA/WPA2 since it is much easier than establishing the necessary RADIUS, supplicant and certificate authority architecture needed for WPA-Enterprise authentication. Cowpatty can implement an accelerated attack if a precomputed PMK file is available for the SSID that is being assessed.
News
July 03 2009
Posted a new version of coWPAtty (4.6) with the following changes:
- Fixed buffer overflow on modern OpenSSL systems when caching hashed hmac-sha1 ipad and opad values (just stupidity on my part, not an exploitable vulnerability);
- Corrected compile warnings with modern gcc.
Special thanks to Kevin Kestinggolrer, Philipp Schroedel, Max Moser, Nathan Grennan, Jason Franks and Michal Knobel for their help and support.
June 04 2009
Posted a new version of coWPAtty (4.5) with the following changes:
- Hashfile can be read from STDIN (thanks Thomas d’Otreppe);
- More liberal collection of handshake information to make coWPAtty work with AP’s that do not implement the 4-way handshake exactly to the specification. This is not the default, but can be turned on with “-2” (thanks to Nathan Grennan);
- Can process a dictionary or hashfile attack when only the 1st and 2nd frames of the 4-way handshake are present, making it easier to attack an exchange even when the full 4-way handshake was not observed (e.g. you were channel hopping, and only caught part of the exchange). This could be an issue if the person you are attacking did not have the correct PSK on their system, but I think that is unlikely. This feature is enabled (along with Nathan’s nonstrict patches) with “-2”, try using this if coWPAtty displays the “incomplete four-way handshake exchange” message;
- Added support for validating that the needed handshake information is present (either with all four frames of the handshake, or frames 1 and 2 with the “-2” option). Thanks to Pure Hate for his support on this;
- Fixed NULL dereference bug when processing radiotap captures (thanks to Michal Knobel).
My apologies for not maintaining coWPAtty with more regularity, though I sincerely appreciate the bug reports and suggestions from everyone. You can get the source for coWPAtty 4.5 below.
March 20 2008
Posted a new version of coWPAtty (4.3) with the following changes:
- Added support for IEEE 802.11e QoS frames;
- Added support for Mac OSX and FreeBSD platforms;
- Added “make install” support;
- Removed OpenSSL-independent MD5 support for WPA networks, OpenSSL is now mandatory for coWPAtty.
Code available in the download section below. Thanks to Dennis Herrmann for the FreeBSD support patch, Thomas d’Otreppe for the “make install” patch, and to Andrew von Nagy for sample QoS packet captures.
October 3 2007
Robin Wood posted a patch for coWPAtty to let it handle radiotap-formatted capture files. Unfortunately, this did not work very well, as the radiotap header can vary in length across different drivers, and can even change during a single packet capture session.
I’ve updated coWPAtty to a new version to support all versions of radiotap capture files. See the download section below.
Screenshots
Download
coWPAtty 4.6
Linux source (104K, MD5: b90fd36ad987c99e7cc1d2a05a565cbd)
README
coWPAtty 4.5
Linux source (103K, MD5: 13e13c79ce6f5695dae355792b80d8aa)
README
coWPAtty 4.3
Linux source (103K, MD5: deccac0763a05ef7014107d347bf9190)
README
coWPAtty 4.2
Linux source (106K, MD5: 35cfd867940efccae3dcec081b19221a)
README